WHY CYBER SECURITY?
IT’S NOT A MATTER OF IF, IT’S WHEN
We are the only organization that leverages our ERP and Cybersecurity expertise to provide maturity to the business intelligence platforms, Big Data, AI and IoT.
WHAT WE DO
CUSTOMIZED CYBER SECURITY SOLUTIONS BASED ON YOUR INFRASTRUCTURE
We provide advisory, transformation, implementation and managed security services to help you mitigate risks to take full advantage of advanced technologies and proven risk management models.
Our practical solutions are specifically tailored to your industry and business needs. Let our team of exceptionally experienced security professionals help you build resilience across traditional networks, infrastructures and all endpoints (including cloud, mobile and the Internet of things).
Managed Services
Managed Security Services (MSS) offering capabilities to Detect, Protect, Respond and Recover critical business data. Some solutions we offer include intrusion detection systems, intrusion prevention systems, malware blocking capabilites, Business Intellegence (BI) platforms.
Learn More
Corporate Training
Building in-house capabilities through customized training programs to strengthen security profile of an organization. Establishing governance to effectively measure the risk profile of an organization by ensuring proper metrics are in place. We design customized training modules based on the assessment of the infrastructure.
Learn More
Staffing Solutions
Zartek specializes in human capital needs assessment of an organization to provision required expertise through staff augmentation.
Learn MoreINCREASING COSTS OF CYBER ATTACKS
The percentage increase in cyber crime costs between 2016 and 2017 as measured. The IT industry has experienced significant increases in total cyber crime.
Legend
Mean = 26.4%
n = 254 companies


COSTLY CONSEQUENCES
CYBER ATTACKERS ARE EVOLVING
Over the last two years, the accelerating cost of cyber crime has increased %23 costing organizations US$11.7 million on average, in managing incidents or spending to recover from disruptions to their business and customers. Attackers are getting smarter and finding it easier to develop new tactics to scale cyber crime globally
INCREASING FREQUENCY OF ATTACKS
Average Annualized Attack Frequency
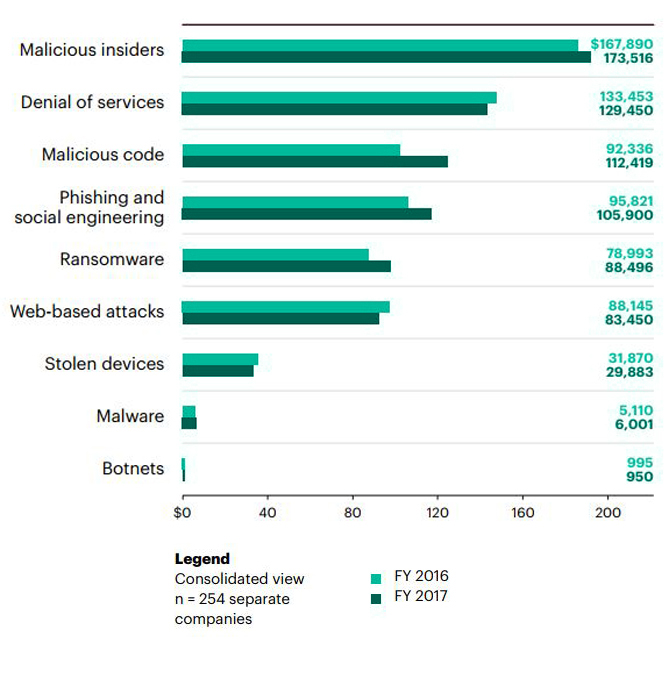
The cost of cyber crime is also influenced by the frequency of attacks. This graph shows the cost of cyber crime and attack frequency. The most expensive attacks are malicious insiders, denial of service and Web-based attacks.
POSITIVE ROI FROM CYBER SECURITY
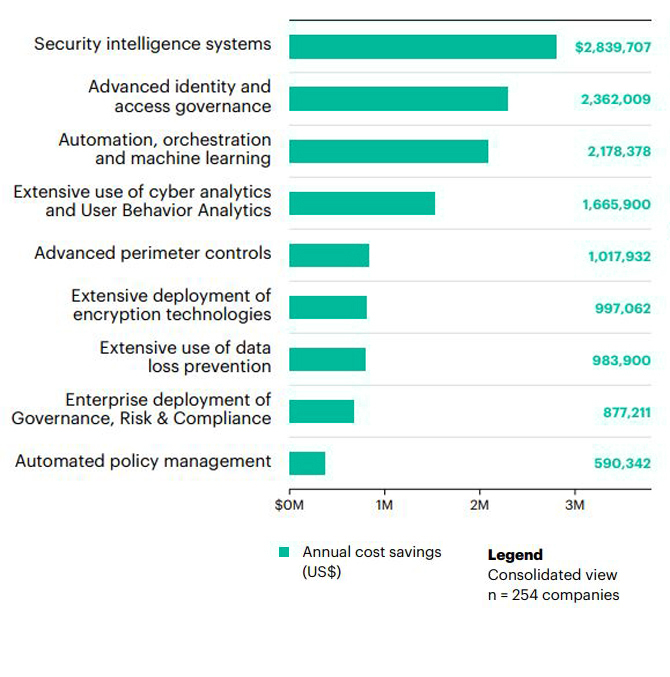
Cost savings by enabling technologies
Investments in various cyber solutions has a positive ROI for organizations. It’s vital to determine the security solutions needed for your organizational needs which will provide the highest cost savings and return on your investments.
CLIENTS















OUR MESSAGES
CTO, Cybersecurity
Many businesses tend to invest & focus more on technology controls rather investing in building expertise to combat cyber threats. These controls have never been enough to stop a sophisticated attacker with malicious intent. It is best to establish requirements for risk tolerance and set risk appetite holistically for critical business processes, handling sensitive information and to educate users to follow strict policies laid out in the governance process.
CTO-SAP
Big data and SAP go hand and hand but what nobody talks about is, how crucial cybersecurity element is in SAP. At ZARTEK we have achieved a workflow and a proven state of the art system that help provide ERP/SAP solutions to enterprises/our client but also do it with the highest security protocols and standards.
Today's technology advancement may not be the latest by tomorrow, so as the techniques & tools being used by hackers. Majority of the companies rely on basic firewalls, anti-virus software & SSL to protect their sensitive data records whereas, hackers treat these protection tools as a toy off the shelves. We at Zartek not only construct the most robust security vault around the systems but keep ahead of the possibilities of breaches & vulnerabilities by deploying 24/7 highly advanced threat detection, risks, mitigation, and protection monitoring mechanism known as SCS (Security Compliance System) by Zartek.
WHO WE WORK WITH
GLOBAL PARTNERS







LEARN. IMPLEMENT. PROTECT.
KNOWLEDGE CENTER
Are You Prepared to Tackle Cyber Attack?
Cyber attacks are going to happen and your response plan will directly affect your overall security and gravity of the assault itself. In today’s digital…
Why is Cybersecurity Important?
In 2014, the world was exposed to an unauthorized glimpse inside entertainment giant Sony Pictures. Confidential information, including personal information about employees of Sony, executive…
It’s never too late to Strengthen Your Security
IDC’s latest report highlighted that 84% of organisations across Asia Pacific1 are operating with less-than-ideal IT security strategies in place2. This is today’s cyber reality;…